RT7xx - OTA update by using SB3 file#
In this walkthrough, if possible, the lifecycle of the device is not changed for development purposes, so the device can be restored to its initial state. In real scenarios, transitioning the chips to the corresponding lifecycle is based on specific requirements.
Common information related to SB3 is available in the documentation ‘OTA update by using SB3 file’.
1. Provisioning of the device - initial setup#
The device must be provisioned to support SB3 processing. To simplify the workflow, the MCUXpresso Secure Provisioning Tool (SEC tool) is used.
RT7xx family supports shadow registers to process SB3 files for development purposes, so there is no need to advance lifecycle.
To provision the device perform the following steps:
Erase the device
Build
mcuboot_opensource+ota_mcuboot_basicorota_rom_basicproject depending what you want to evaluateGet the device into ISP mode
Typically on development boards hold the ISP button and press the reset button
Open the SEC tool and create new workspace for RT7xx target device
Test the ISP connection in SEC tool (Target -> Connection…)
Setup and test debug probe (Target -> Debug Probe…)
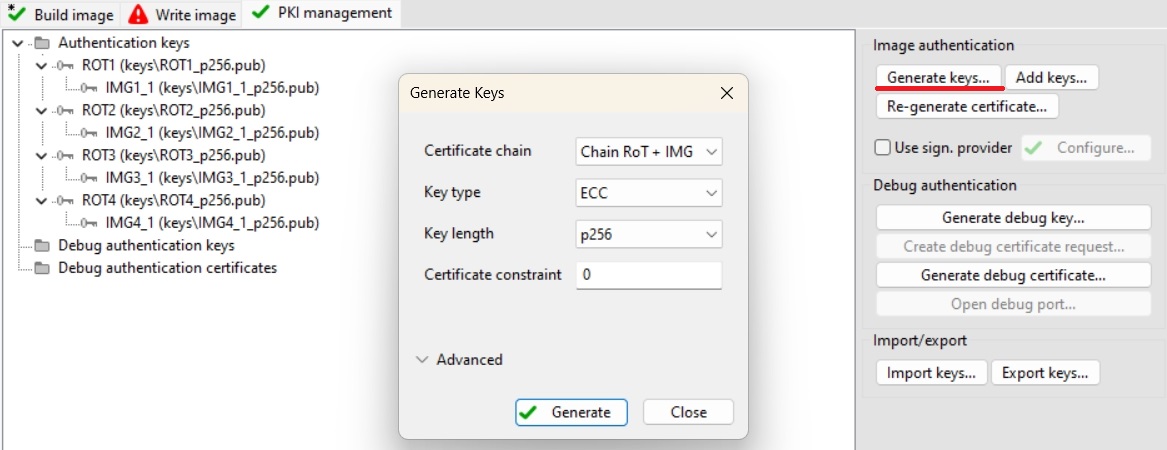
Switch to PKI management tab
Click Generate keys (leave default settings) and then switch back to Build image tab
(Optional) Let ROM generate FCB
Target -> Boot Memory (or CTRL+B)
Select Boot memory type -> XSPI NOR - simplified
Click Convert to complete FCB, check option Apply the converted FCB as the boot device configuration and then click Convert
Initial setup
Boot: Plain signed
Note: Uncheck option with replacing FCB, if you proceeded the step 6
Lifecycle: Develop, shadows
Select an authentication key and generate CUST_MK_SK and OEM SB seed
For MCUboot use case:
Select
mcuboot_opensourceoutput binary or ELF image as Source executable imageClick Additional images
Check Image 1 and set a path to an image of signed application
ota_mcuboot_basicNote: This initial image has to be generated with additional
--pad --confirmimgtool argumentsSet Target address
0x28040000(seeflash_partitioning.h) to place this initial image in primary slot
For ROM only use case:
Select
ota_rom_basicoutput binary or ELF image as Source executable imageClick Dual image boot
Set Target dual boot image to Image 0
Set Image 1 offset to 0x400000 (4MB)
Set Image 1 size to Same as offset
Click OK
Click Firmware versions
Set initial image firmare version 1 (this number is evaluated by ROM during boot when selecting the image with the highest version)
Click OK
Click Build image

Write image tab
Click Write image
Switch boot from ISP to normal boot (XSPI0) and soft reset the board
Now the device is provisioned with RKTH and CUST_MK_SK using shadow registers without transition of the lifecycle. The shadow registers are preserved and re-initiated during soft reset (without power-cycle).
2. Prepare OTA images#
RT7xx uses flash remapping feature using overlay mechanism (see ‘MCUboot and flash remapping feature’). For this reason we have to prepare an ota image targeting currently inactive image slot. Following steps assume that primary slot (or image 0) is active and we have to prepare an OTA image targeting second slot (or image 1)
2.1 ROM only use case#
Flash memory layout with 4MB image offset looks like this:
Partition |
offset |
size |
|---|---|---|
FCB |
0x28000000 |
0x004000 |
Image 0 |
0x28004000 |
0x400000 |
Image 1 |
0x28400000 |
0x400000 |
Switch to Build Image tab
Increase image version using Firmware versions to number 2 and click Build image
Open Tools -> SB Editor (CTRL + E)
Click Import from workspace to initialize an template for adjustment
Rework command sequence into these commands:
configureMemory - configAddress: 0x28000000 memoryId: $memoryId
erase - configAddress: 0x28400000 size: $(appEraseSize) memoryId: $memoryId
Note: erase command, depending on erase size, is a blocking process and could leave the device in an unresponsive state for a longer period of time. It’s recommended to let the application the erase before processing OTA SB file.
load - configAddress: 0x28400000 memoryId: memoryId data: ${appPath}
Change name of secure binary file to
ota_rom_image1.sbClick Generate

Same steps can be used for an ota image targetting the image 0 slot with these adjustments:
Image version has to be higher than active one in the image 1 slot
configAddress: 0x28004000
2.2 MCUboot bootloader use case#
Flash memory layout according settings in flash_partitioning.h should look like this:
Partition |
offset |
size |
|---|---|---|
FCB + MCUBOOT |
0x28000000 |
0x040000 |
Primary slot |
0x28040000 |
0x200000 |
Secondary slot |
0x28240000 |
0x200000 |
Switch to Build Image tab
Sign
ota_mcuboot_basicusingimgtoolwith higher image version as usual by following steps in specificexample_board_readme.mdfor your board.Open Tools -> SB Editor (CTRL + E)
Click Import from workspace to initialize an template for adjustment
Rework command sequence into these commands:
configureMemory - configAddress: 0x28000000 memoryId: $memoryId
erase - configAddress: 0x28400000 size: 0x200000 memoryId: $memoryId
Note: erase command, depending on erase size, is a blocking process and could leave the device in an unresponsive state for a longer period of time. It’s recommended to let the application the erase before processing OTA SB file.
load - configAddress: 0x28240000 memoryId: memoryId data: path to signed
ota_mcuboot_basic
Change name of secure binary file to
ota_mcuboot_secondary_slot.sbClick Generate

Same steps can be used for an ota image targetting the primary slot with these adjustments:
Image version has to be higher than active one in the secondary slot
configAddress: 0x28040000
3. Firmware update#
For demonstration purpose we use ExtraPutty tool as this fork of classic Putty has XMODEM support. Alternatively TeraTerm can be used.
Note: Keep in mind that hard reset invalidates shadow registers.
3.1 ROM bootloader only use case#
Run the initial
ota_rom_basicapplicationCheck image state and active flag location with
imagecommandSee active flag location to specify inactive image slot
Send the OTA image
Run
xmodem_sb3commandSend
ota_rom_image1.sbtargetting inactive slot via Files Transfer/Xmodem (1k)
Reboot the device with
rebootcommandCheck image update with
imagecommand
Here is an example of serial output:
*************************************
* Basic ROM application example *
*************************************
$ image
Flash REMAP_OVERLAY disabled
IMAGE 0:
<IMG_VERSION 0x1 LENGTH 36820 EXEC_ADDR 0x28004000>
*ACTIVE*
IMAGE 1: Invalid image header
$ xmodem_sb3
Started xmodem processing SB3
Initiated XMODEM-CRC transfer. Receiving... (Press 'x' to cancel)
CCCC
Received 42880 bytes
SB3 has been processed
$
$ reboot
System reset!
*************************************
* Basic ROM application example *
*************************************
$ image
Flash REMAP_OVERLAY active
IMAGE 0:
<IMG_VERSION 0x1 LENGTH 36820 EXEC_ADDR 0x28004000>
IMAGE 1:
<IMG_VERSION 0x2 LENGTH 36820 EXEC_ADDR 0x28004000>
*ACTIVE*
$
3.2 MCUboot bootloader use case#
Run the initial
ota_mcuboot_basicapplicationCheck image state and active flag location with
imagecommandSee active flag location to specify inactive image slot
Erase inactive slot with
image erasecommandNote: not needed if the SB file contains the erase command
Send the OTA image
Run
xmodem_sb3commandSend
ota_mcuboot_secondary_slot.sbtargetting inactive slot via Files Transfer/Xmodem (1k)
Mark installed image ready for test
Run
image testcommand
Reboot the device with
rebootcommandCheck image update with
imagecommandMark the updated slot with confirm flag using
image acceptand check the state again withimagecommand again
hello sbl.
Bootloader Version 2.2.0
Primary slot: version=1.0.0+1000
Image 0 Secondary slot: Image not found
Image 0 loaded from the primary slot
Bootloader chainload address offset: 0x40000
Reset_Handler address offset: 0x40400
Jumping to the image
Booting the primary slot - flash remapping is disabled
*************************************
* Basic MCUBoot application example *
*************************************
Built Oct 3 2025 20:33:10
Toolchain IAR ANSI C/C++ Compiler V9.70.1.475/W64 for ARM
$ image
Image 0; name APP; state None:
Slot 0 APP_PRIMARY; offset 0x40000; size 0x200000 (2097152):
<IMAGE: size 42421; version 1.0.0+1000>
SHA256 of image payload: E069B6127A708EE88B39...
log_addr 0x28040000
*ACTIVE*
Slot 1 APP_SECONDARY; offset 0x240000; size 0x200000 (2097152):
<No Image Found>
$ image erase
Erasing inactive slot...done
$ xmodem_sb3
Started xmodem processing SB3
Make sure this device is provisioned to accept secure binary and its load address is 0x240000
Initiated XMODEM-CRC transfer. Receiving... (Press 'x' to cancel)
CCCCC
Received 51200 bytes
SB3 has been processed
$
$ image test
write magic number offset = 0x43ff00
$ reboot
System reset!
hello sbl.
Bootloader Version 2.2.0
Primary slot: version=1.0.0+1000
Secondary slot: version=1.1.0+1000
writing copy_done; fa_id=1 off=0x1fffe0 (0x43ffe0)
Image 0 loaded from the secondary slot
Bootloader chainload address offset: 0x240000
Reset_Handler address offset: 0x240400
Jumping to the image
Booting the secondary slot - flash remapping is enabled
*************************************
* Basic MCUBoot application example *
*************************************
Built Oct 3 2025 20:33:10
Toolchain IAR ANSI C/C++ Compiler V9.70.1.475/W64 for ARM
$ image
Flash REMAP_OVERLAY active.
Image 0; name APP; state Testing:
Slot 0 APP_PRIMARY; offset 0x40000; size 0x200000 (2097152):
<IMAGE: size 42421; version 1.0.0+1000>
SHA256 of image payload: E069B6127A708EE88B39...
log_addr 0x28040000 remaps to 0x28240000
Slot 1 APP_SECONDARY; offset 0x240000; size 0x200000 (2097152):
<IMAGE: size 42421; version 1.1.0+1000>
SHA256 of image payload: E069B6127A708EE88B39...
log_addr 0x28240000 remaps to 0x28240000
*ACTIVE*
$ image accept
$ image
Flash REMAP_OVERLAY active.
Image 0; name APP; state Permanent:
Slot 0 APP_PRIMARY; offset 0x40000; size 0x200000 (2097152):
<IMAGE: size 42421; version 1.0.0+1000>
SHA256 of image payload: E069B6127A708EE88B39...
log_addr 0x28040000 remaps to 0x28240000
Slot 1 APP_SECONDARY; offset 0x240000; size 0x200000 (2097152):
<IMAGE: size 42421; version 1.1.0+1000>
SHA256 of image payload: E069B6127A708EE88B39...
log_addr 0x28240000 remaps to 0x28240000
*ACTIVE*
$
